How I Tame OKX: Login, Trading, and Wallet Tips from Real Use
Whoa! Okay, so check this out—I almost missed a login quirk on OKX. I’m biased, but secure logins have been bugging me lately. Initially I thought the process was just two-step authentication, but then realized there are subtle device-linked verifications and session tokens that change depending on whether you use the app, web, or API integrations. This matters if you trade fast or use advanced orders.
Seriously? My first impression was that login delays were network issues. But sometimes a new security prompt appears only on desktop. On one hand it’s reassuring because added checks mean fewer account takeovers, though actually it can break automated scripts or API sessions if your keys or cookies aren’t handled just so. Here’s the thing: document your devices and session flows.
Hmm… If you’re in the US you might see additional KYC steps at high withdrawal thresholds. That surprised me the very first time I tested small then large withdrawals. Trading fast on margin without confirming your withdrawal email or whitelisted address can lead to agonizing delays during market moves, and yes I’ve sat through that panic more than once. Something felt off about the UX flow at times.
Wow! Okx’s wallet integration makes transfers smoother than many exchanges. But wallet names and networks must match exactly or funds go nowhere. When I moved assets between my hardware wallet and the OKX wallet I double-checked the chain and gas token, because swapping ERC20 tokens to a BSC address is not a fun ‘oops’ to reverse and recoveries are messy and sometimes impossible. Label your addresses and keep encrypted backups offline for emergencies.
Want a quick setup check? Start here
For a practical walkthrough when setting up your account or troubleshooting, I recommend checking the official guides and step-throughs at okx—they helped me map flows I hadn’t considered. I trade derivatives sometimes and latency truly matters to my P&L. OKX supports advanced order types and futures, but also requires you to configure API permissions carefully. Initially I thought broad API keys were convenient, but then realized restricting trade-only keys and disabling withdrawals on API keys was a small step that prevented a big headache when a script misbehaved. My instinct said keep it minimal and separate accounts for bot trading.
I’m not 100% sure, but some features are rolled out regionally and are not identical between app and web. That can be frustrating when you need a margin setting that lives only in the app. On the analytical side, it’s helpful to keep a changelog of your own—note when you update devices, browsers, or the app version—because then you can correlate unexpected prompts or lockouts to a specific change instead of guessing in the dark. I keep a private spreadsheet and brief notes for every significant change.
Whoa! Security settings deserve periodic review, especially your withdrawal whitelists and MFA options. There’s a human side too; customer support response time varies. If you ever face a locked account the fastest path is to gather screenshots, timestamps, transaction IDs, and any verification emails before contacting support, because the more evidence you bring, the less back-and-forth you’ll endure. Also, enable login alerts and monitor IP activity through your account dashboard.
Really? Fees and maker-taker structures can confuse new traders, and pricing changes over time. Watch for fee tiers tied to 30-day volume or token-based discounts. Through my own trading I found that moving volume between spot and derivatives without checking fee brackets caused small losses that compounded over dozens of trades, which taught me to monitor effective fees as much as strategy edge. Pro tip: enable fee discounts and lock in VIP tiers if you trade often.
Oh, and by the way… the wallet browser extension and the native OKX wallet behave slightly differently. Backup seeds belong offline and split across secure locations. During one test transfer I almost used a wrong token standard and although there was a recovery option it required support intervention and proof, which cost time and stress and a fair bit of patience. Document your seed phrase procedure and practice restorations in a safe environment.
Okay. If you use third-party wallets or routers carefully vet the bridge or contract. Smart contracts are unforgiving; read the approvals and allowances. Actually, wait—let me rephrase that: consider setting low allowances and only increasing them when needed, then revoke permissions after swaps to reduce attack surface and make audits simpler. This level of hygiene will save you headaches much later on.
I’m biased, but I prefer using hardware wallets for large holdings. Cold storage plus a hot wallet for active trades strikes a good balance. On the edges, smaller accounts or fresh addresses for algorithmic bots reduce blast radius if credentials leak, and segregating funds according to function cuts recovery complexity when things go south. Also consider insurance or custodial services for institutional scale.
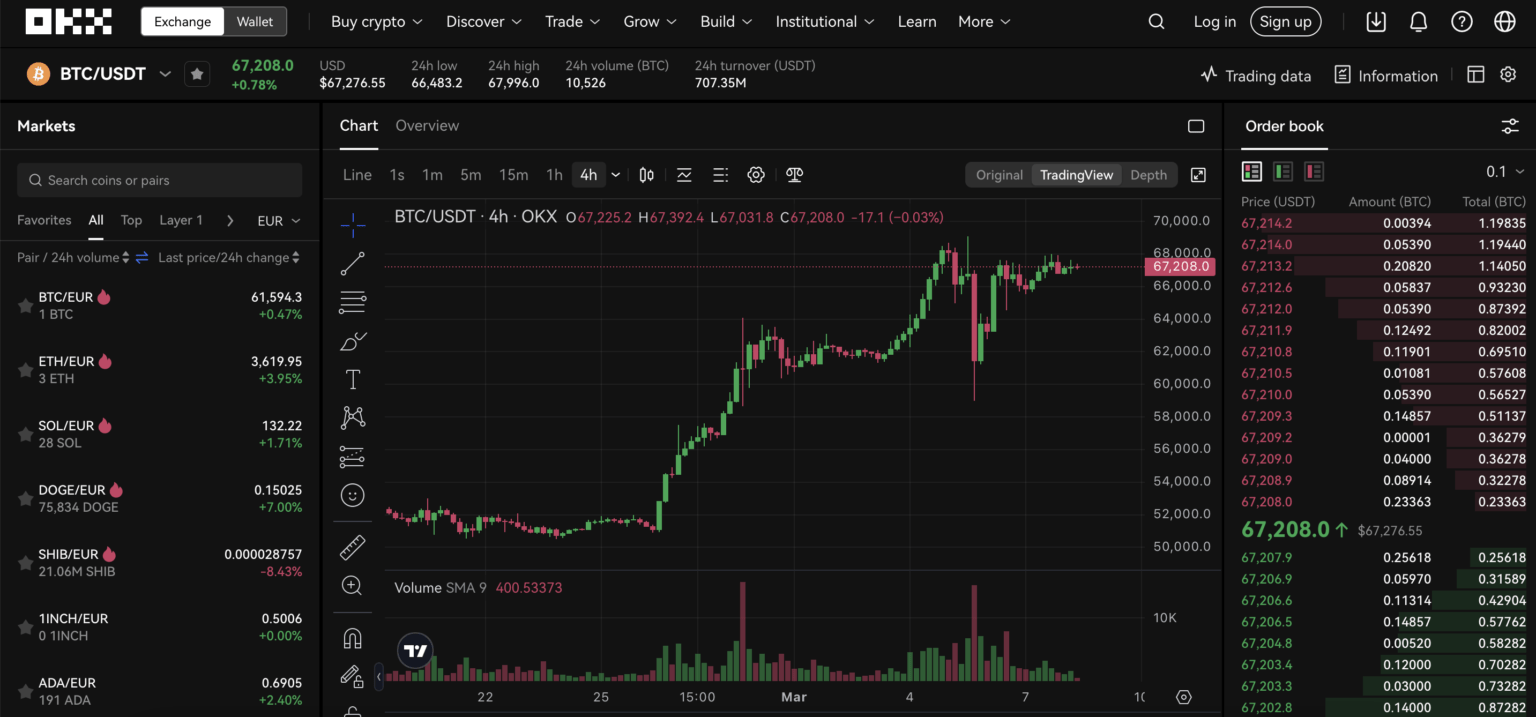
Seriously. For day traders, UI responsiveness and charting matter a lot. OKX’s order book depth and liquidity compete well with major platforms. If you plan to use advanced charting or alarm systems integrate them with your execution environment cautiously, because mismatches in candle timeframes, API polling rates, and order types can create costlier friction than you expect. Finally, read the small print on margin requirements and liquidation rules.
I’ll be honest—navigating OKX login, trading, and wallet features feels like managing a small fleet. On the one hand it’s a powerful ecosystem with competitive fees and product breadth, though on the other hand the complexity means you must be deliberate about keys, settings, and recovery plans if you value uptime and security. Check your devices, test withdrawals with tiny amounts, and automate alerts. Somethin’ like that saved my bacon more than once, very very important…
FAQ
How do I speed up login issues?
Clear browser cache, confirm device authorizations, and try the mobile app if web keeps prompting you. Keep MFA methods current and consider authentication apps over SMS for reliability. If using API, reissue keys with narrow permissions rather than broad keys after a problem.
Can I recover a mistaken token transfer?
Sometimes, but not always. Recovery often depends on whether the receiving contract supports token returns and whether the exchange’s internal processes can act. Prepare proofs and reach support quickly; split test transfers reduce risk.


Deja una respuesta